Command Prompt is a powerful tool that an Operating System offers to its users. It is the portal through which anything can be accessed and controlled on your PC or laptop. It exists across operating systems like Windows, Mac, Linux, etc. But today, we are going to look at the lesser-known commands that can be used while you try your hand at hacking.
Table of Contents
10 Best CMD Hacking Commands
But before we start off, you will have to learn how to enable NetBios.
- Simply open your Network Connection and select Properties.
- Under that, choose TCP/IP, and then select Properties again.
- Proceed to press the Advanced and WINS tab respectively, and finally select Default for NetBIOS.
- That is it. You are set to use NetBIOS on the Command Prompt now.
Net user
This command is used to reset the Windows operating system’s user password in case it has been forgotten, or just unknown.
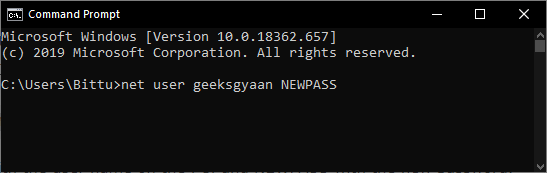
Syntax
net user USERNAME NEWPASS
(Replace USERNAME with the user name on the PC, and NEWPASS with the new password. Press enter to execute it.)
If you are getting access denied message then run command prompt as administrator.
Ping
This command is to be used when checking if the host that you are pinging is live or offline. If it is live, it means that the host is working at the time the ping command is executed. You can execute this in two ways:
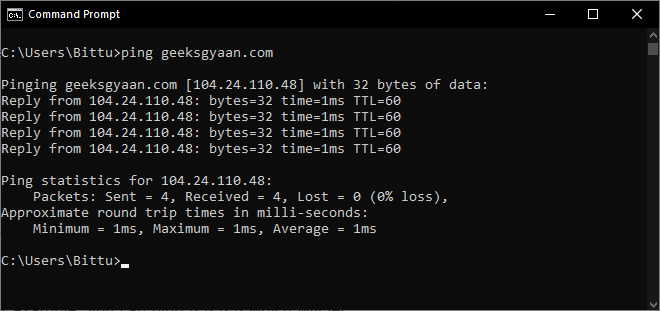
ping x.x.x.x (where x is the IP address).
For example, you can ping 8.8.8.8 which will let you know if Google is live
Or, in case you do not know the IP address of the host, you can also input the web address. For example:
ping www.geeksgyaan.com
Nslookup
This is a popular command executed when trying to resolve DNS into IP. For example, when you know the URL of a website but not the IP address, this command will help you to find the IP address of a website. For example,
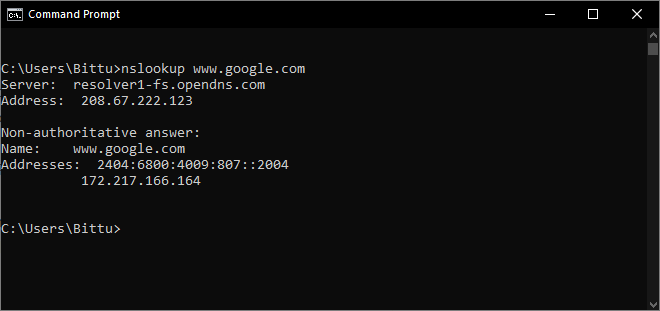
nslookup www.google.com
This will return the IP of the given website.
Another useful functionality of this command is for when you want to find out the IP address of specific mail servers. For example, if you wish to check the servers of Yahoo, just input:
nslookup (press enter)
set type=mx (press enter)
yahoo.com
Tracert
This lets the user obtain information on the jumps that a packet of data goes through before reaching the final destination. Basically it traces the route that a packet takes as it is trying to reach where it is supposed to go.
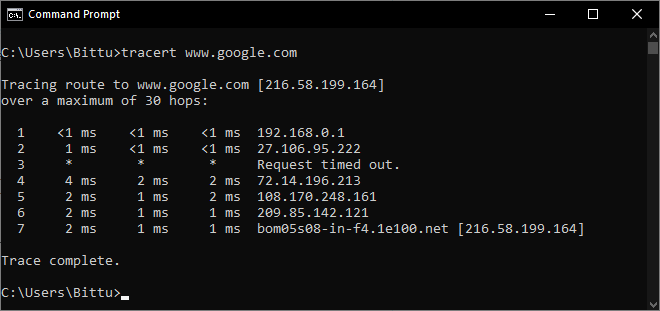
The syntax for this is
tracert x.x.x.x (with x being the IP address)
tracert www.google.com
Again, in case you do not know the IP for the website you wish to trace.
Read – 25 Best Hacking Apps for Android
Arp
Arp stands for address resolution protocol. Executing this command displays and modifies the entries in the ARP cache, which contains one or more tables that are used to store IP addresses. This command is useful when you are trying to figure out if anyone’s altered arp in your LAN by using this very command.
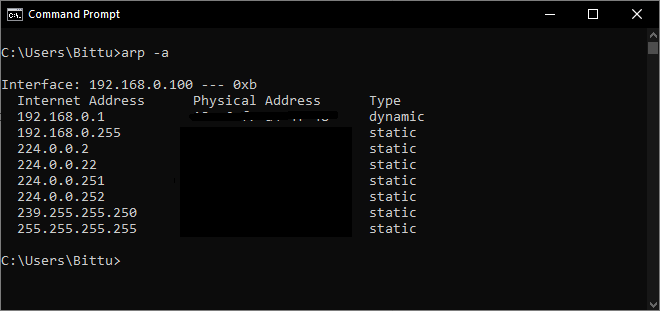
Syntax:
arp -a
Route
Route command displays information regarding the routing table, gateway information, interface, and metrics.
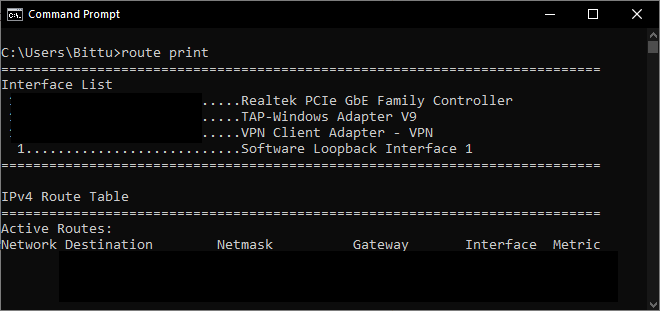
Syntax:
route print
IPconfig
This command is possibly one of the most frequently executed ones because it is so helpful regarding retrieving various information regarding your network. It provides information on your IP address, Gateway, the DNS you are using and such.
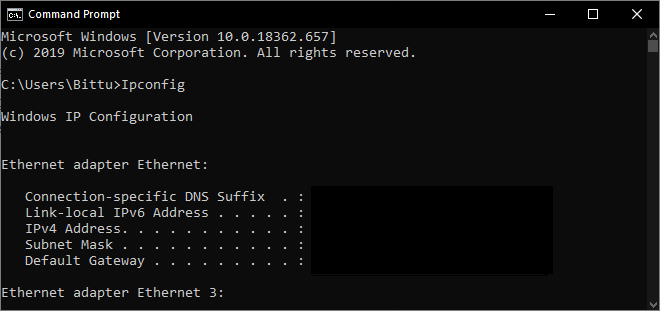
Syntax:
ipconfig
Or
ipconfig /all (when trying to retrieve information for all networks)
In case you have dynamic IP but wish to change it, just execute
ipconfig /release (which will release the IP)
ipconfig /renew (which will proceed to renew your IP)
Net view
Execute this command to know more about the resources, computers or domains that are currently being shared by the Windows device you are using.
Syntax
net view x.x.x.x (with x being the IP address)
net view computername
Read – 15 Vulnerable Sites You Can Legally Hack (Websites for Hacking)
Netstat
This command displays information regarding your network connection.
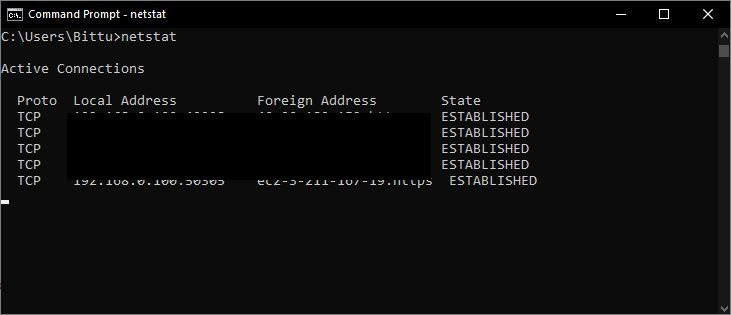
Syntax:
netstat
or
netstat -a
Used for specifically showing all the listening ports and connection with DNS names.
netstat -n
Used for specifically displaying all the open connections with IP addresses.
netstat -an
Used to display information from both the above commands.
net view x.x.x.x (x is the IP address)
net view computer-name will then list the available sharing folders on the target box.
Read – 5 Command Prompt Tricks That Will Make Your Life Easier
Tasklist
This command is meant to be executed when you wish to open the Windows task manager on the Command Prompt. It displays all the processes being run on the device.
Additionally, you can use the command ‘taskkill’ if you wish to specifically end a process that could be unresponsive or is taking up too much resource. For example, let’s kill PID 724.
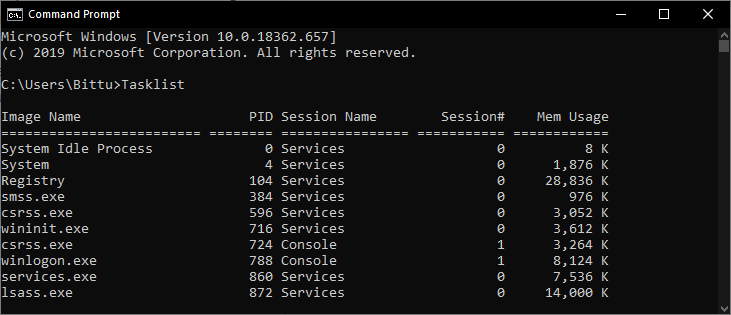
Syntax
taskkill /PID 724 /F
Help command
This is a universal addition to everything. By executing this command following another command in the line, it displays the functionality of the first command. For example, execute
whattevercommand /help
to know the function of whattevercommand. Another syntax of this command is
whatevercommand /?
So there you have it, simple but very efficient commands to be executed whenever you need information and commands that will aid you when trying to understand the networking better, or for your hacking needs.






One other important aspect is that if you are a mature person, travel insurance with regard to pensioners is something you need to really look at. The more mature you are, greater at risk you’re for making something negative happen to you while in another country. If you are not covered by a number of comprehensive insurance coverage, you could have a few serious difficulties. Thanks for discussing your suggestions on this web site.